Security isn’t a feature.
It’s our foundation.
Your customers share their personal details, account data, and emotions in every interaction. With secure translation, we make sure every word stays private, every system stays compliant, and every connection stays dependable.
Certifications that speak for themselves
Global enterprises choose Language IO because our secure translation standards don’t just meet compliance—they set it. Our platform is built and certified to the highest international benchmarks for data protection and AI governance. Each certification represents a layer of assurance that your data, your customers, and your brand are safe. Certifications aren’t the goal. Trust is.
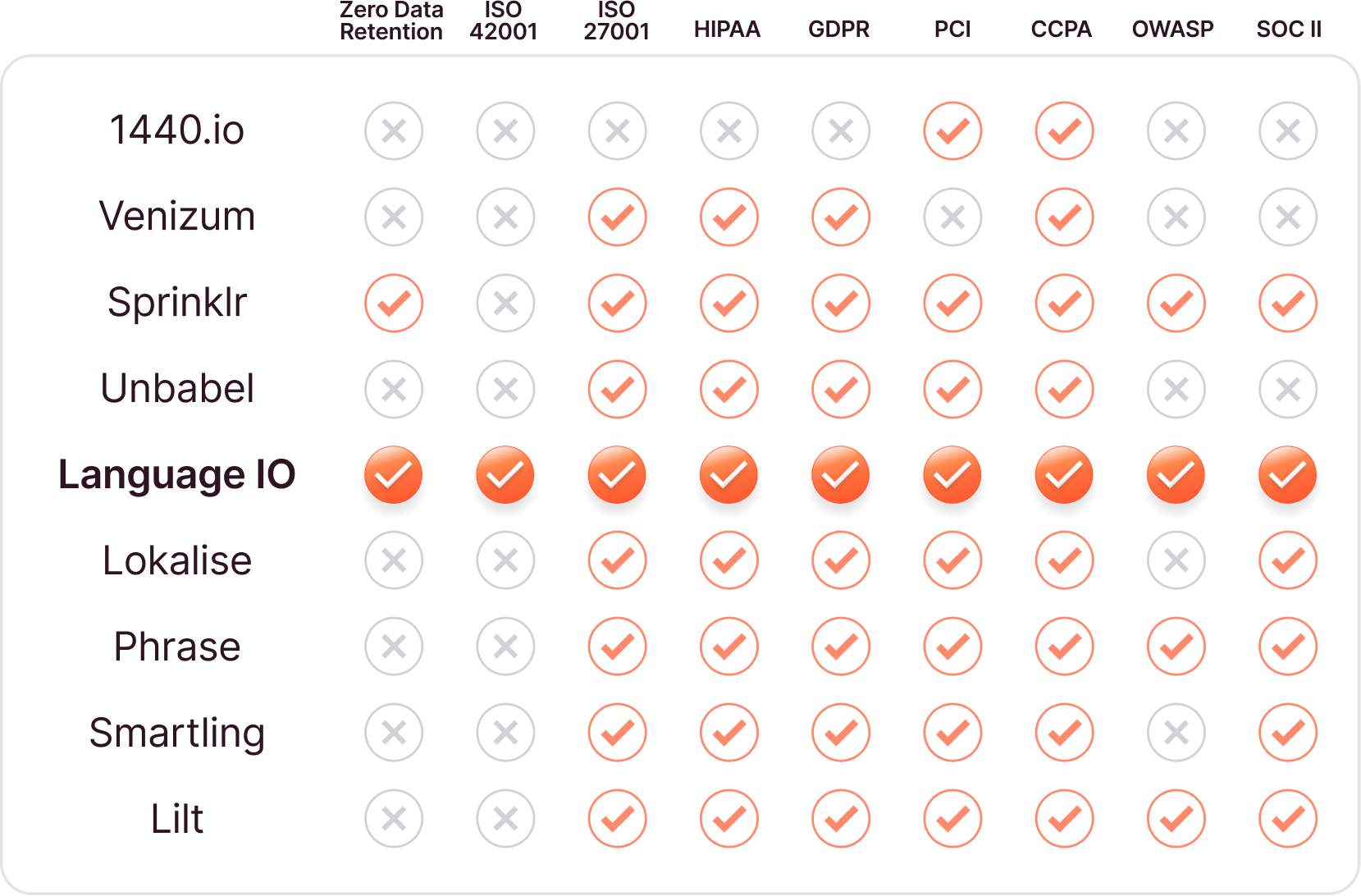
Leading the industry in security standards by every measure.
When it comes to enterprise security, no other translation provider comes close. Language IO is the only platform with true Zero Data Retention, HIPAA alignment, and ISO 42001 readiness, the emerging global standard for AI management. Combined with ISO 27001, SOC II, OWASP, GDPR, PCI, and CCPA compliance, it’s more than a checklist. It’s confidence.
Competition
Our platform is built and certified to the highest international benchmarks for data protection and AI governance.
Each certification represents a layer of assurance that your data, your customers, and your brand are safe.
Language IO Achieves ISO 42001: Setting the Standard for Responsible AI Translation
Language IO just became one of the first translation technology providers in the world to achieve ISO/IEC 42001 certification, the new international standard for responsible AI management.
Zero Data Retention. Total peace of mind.
Your customers trust you with their data. We make sure it never leaves their side. Language IO is the only translation platform with true Zero Data Retention. Every message is translated in real time inside a secure, ISO-certified environment, then instantly erased. No storage. No training. No trace. That means no risk of exposure, no lingering records, and no uncertainty about where your data lives.
Zero Data Retention isn’t a feature. It’s a philosophy. Because the safest system is the one that forgets.
No Storage
Every translation is processed in real time and never stored on our servers.

No Training
We never use customer data to train models or improve AI performance.

No Trace
Once translation is complete, your data is instantly and permanently deleted.

Trusted by the most regulated industries
From banking to biotech, leading enterprises rely on Language IO to protect every word they translate. Every industry. Every standard. One platform that keeps you compliant, private, and protected.
Core Regulations &
Standards
Vertical-Specific Compliance
What It Means for You
Financial Services
ISO 27001, SOC II, ISO 42001, GDPR, CCPA
PCI DSS

Translations meet global security and privacy rules for every transaction.
Healthcare & Life Sciences
ISO 27001, SOC II, ISO 42001, GDPR, CCPA
HIPAA

Protected health information stays compliant and confidential end-to-end.
Ecommerce & Retail
ISO 27001, SOC II, ISO 42001, GDPR, CCPA
PCI DSS

Customer and payment data are encrypted, regionalized, and never retained.
Technology & SaaS
ISO 27001, SOC II, ISO 42001, GDPR, CCPA
—

Secure, zero-retention architecture that scales with your global platform.
Travel & Hospitality
ISO 27001, SOC II, ISO 42001, GDPR, CCPA
—

Privacy protections built for multinational customer databases and loyalty programs.
At Language IO, security isn’t a milestone. it’s a mindset.
We were first to achieve HIPAA alignment, the only company in our category with true Zero Data Retention, and now we’re leading the way again with ISO 42001 for ethical AI management. Staying ahead of standards means our customers never have to worry about falling behind.

Bill Hastings
Chief Information Security Officer
Translate everything. Expose nothing.
Translate sensitive content without exposing customer data with Secure Page Translator for Chrome.
Secure Page Translator brings Language IO’s enterprise security to every part of your digital experience — from account settings and billing portals to authenticated support pages. Unlike traditional web translation tools that send full page content to external servers, Secure Page Translator processes translations securely within your environment. No data ever leaves your domain. No content is stored. No compliance risk. It’s built for organizations that need to localize sensitive, customer-specific pages without compromising privacy, regulatory compliance, or brand trust.
Questions? We’ve got answers.
FAQs
What makes Language IO’s translation software secure?
Language IO is built with security as a priority at every level. The platform follows worldwide standards and regularly undergoes audits and tests to protect your data. It uses strong privacy controls, real-time translation with zero data stored, and strict access safeguards so your information stays safe while being translated.
How does Language IO protect sensitive or confidential data during translation?
Language IO uses a Zero Data Retention approach. That means every message sent for translation is processed in real time and then immediately deleted – no copies are stored on servers. All data in transit is protected with secure connections, so your sensitive or confidential customer content isn’t kept or reused.
Is Language IO compliant with data protection regulations like GDPR or HIPAA?
Yes. Language IO is fully compliant with the General Data Protection Regulation (GDPR) and has been since the regulation took effect. It also aligns with HIPAA requirements for protecting health information by encrypting data and keeping no lasting records. It supports other privacy standards like CCPA too.
Does Language IO store or log any of the translated content?
No. Language IO does not store or log the content you send for translation. Each translation is done in real time, then immediately erased from the system. This zero retention policy means translations are not logged, saved, or used for training or analytics.
How does Language IO ensure data encryption and privacy?
Language IO uses secure, encrypted connections for all data it processes. It also undergoes regular security testing, including quarterly penetration tests and weekly vulnerability scans, to make sure systems stay strong against threats. These protections help keep data private and secure at every stage.
Can Language IO be used by organizations with strict security requirements?
Yes. Language IO meets high security standards that many enterprises require, including GDPR, HIPAA, and other data protection frameworks. With ISO certifications and regular compliance checks, it’s built for companies that can’t afford to compromise on security.
What security certifications or audits has Language IO completed?
Language IO holds leading security certifications, including ISO 27001:2022 and ISO 42001 for responsible AI. It also undergoes regular SOC 2 audits, penetration testing, and vulnerability scans. These certifications and audits show the platform meets strict international security and privacy standards.